[center]
Windows Internals: Architecture, Processes & Execution
Published 2/2026
Created by B Karthik
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz, 2 Ch
Level: All Levels | Genre: eLearning | Language: English | Duration: 39 Lectures ( 2h 55m ) | Size: 1.91 GB[/center]
Master Windows Internals, WinDbg, PE files, Processes, Threads, Syscalls & Security for Deep System Analysis
What you'll learn
✓ Understand and use WinDbg to analyze Windows processes, threads, and system behavior for both user-mode and kernel-mode debugging
✓ Learn PE file format internals, dissect processes, threads, objects, and handles, and explore how Windows manages these resources
✓ Understand Windows system calls, security tokens, access control, and how applications interact with the kernel
✓ Gain a deep understanding of Windows internals, including Process, Threads, kernel structures and process execution flow
Requirements
● Familiarity with using Windows operating systems, navigating files, and running applications.
● Understanding of at least one programming language (C, C++, or Python recommended) is helpful
● A Windows 10/11 x64 system with WinDbg installed
Description
Welcome to the Windows Internals Course, where you will explore the inner workings of the Windows operating system in depth. This course is designed for security researchers, reverse engineers, penetration testers, malware analysts, and system developers who want to gain a complete understanding of Windows beyond surface-level knowledge.
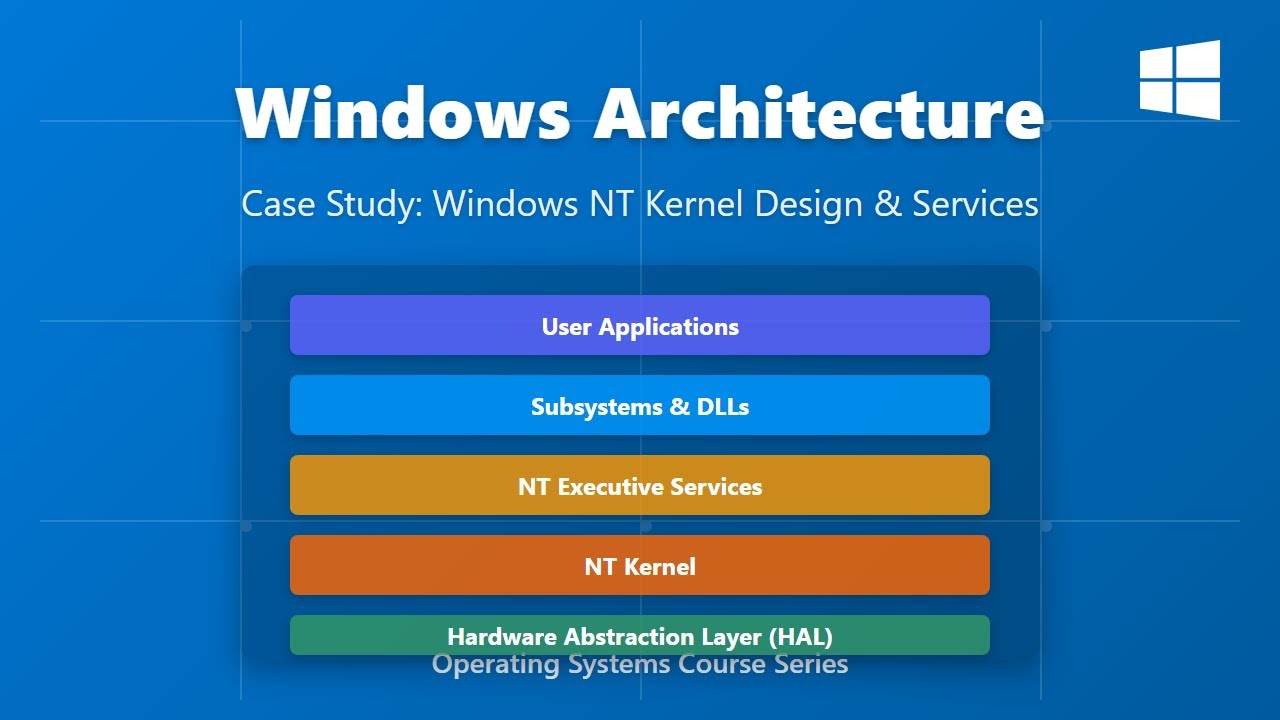
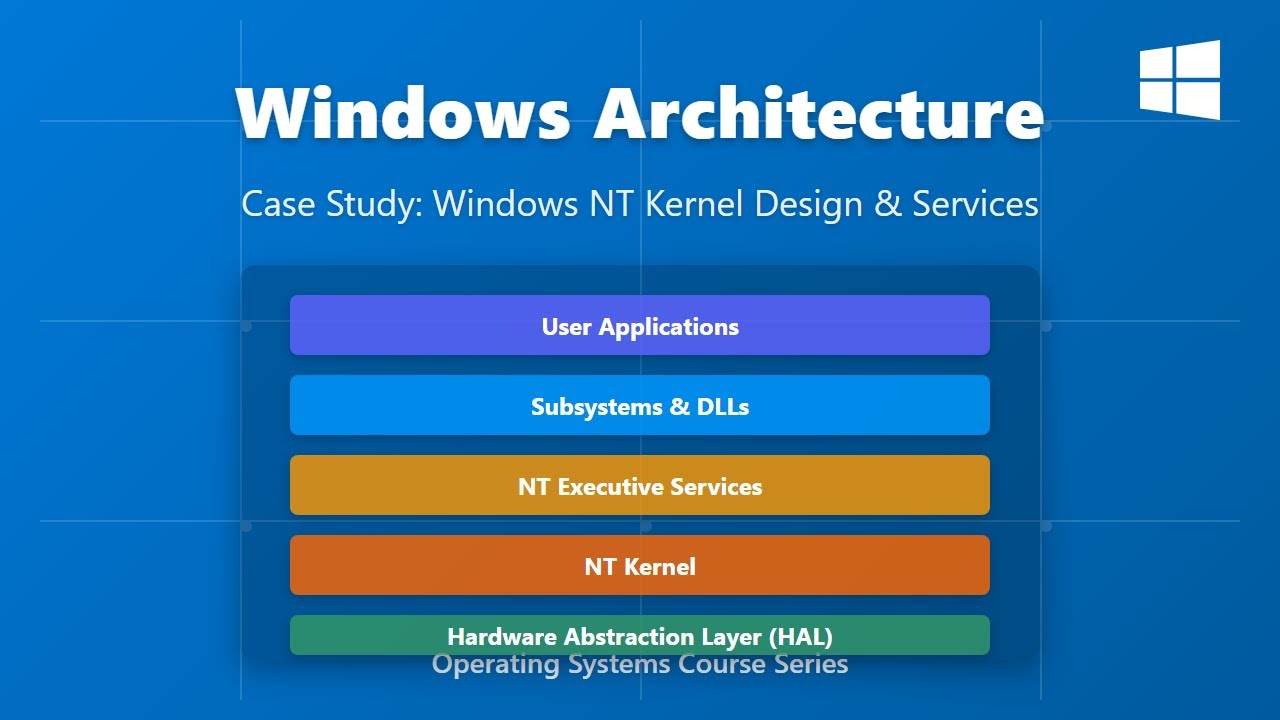
In this course, you will start with an introduction to WinDbg, learning how to navigate and analyze Windows systems effectively. You will then study Windows architecture, process execution, and kernel structures. The course dives into PE (Portable Executable) file internals, providing insights into how Windows executables are structured and loaded into memory.
You will also explore process and thread management, learning how Windows handles execution flows and multitasking at a low level. The course covers objects and handles, explaining how Windows manages system resources and access. You will gain a deep understanding of system calls, including how applications interact with the kernel, and study security tokens to comprehend access control and permissions. Finally, you will examine interrupts and exceptions, exploring how Windows handles errors and system events at the core level.
By the end of this course, you will have a strong theoretical and practical understanding of Windows internals, enabling you to analyze, debug, and understand Windows behavior like a professional. This course equips you with the knowledge needed for reverse engineering, malware analysis, system programming, and advanced security research.
Who this course is for
■ Reverse engineers and security researchers looking to master process, thread, and kernel-level analysis.
■ Penetration testers and ethical hackers aiming to understand Windows internals for offensive and defensive security.
■ Students or IT professionals interested in building a strong foundation in Windows architecture, debugging, and system-level programming.